COMPLIANCE & SECURITY
COMPLIANCE & SECURITY
COMPLIANCE & SECURITY
1. Regulatory Posture
1.1 We operate under Hong Kong law. Corporate matters are governed by the Companies Ordinance (Cap. 622). Personal data is handled under the PDPO (Cap. 486).
1. Regulatory Posture
1.1 We operate under Hong Kong law. Corporate matters are governed by the Companies Ordinance (Cap. 622). Personal data is handled under the PDPO (Cap. 486).
2. Privacy Governance
2.1 We implement a privacy management program aligned with PCPD best practice. Hong Kong law does not mandate appointment of a Data Protection Officer, but we designate responsible personnel for privacy oversight and compliance.
2. Privacy Governance
2.1 We implement a privacy management program aligned with PCPD best practice. Hong Kong law does not mandate appointment of a Data Protection Officer, but we designate responsible personnel for privacy oversight and compliance.
3. AML/CFT (where our Services involve financial activity)
3.1 We apply a risk-based program aligned with Hong Kong’s Anti-Money Laundering and Counter-Terrorist Financing Ordinance (Cap. 615) and regulator guidelines, including customer due diligence (CDD), ongoing monitoring, record-keeping, and suspicious transaction reporting where applicable. We also follow sector-specific guidance (e.g., HKMA, SFC, Companies Registry) where relevant.
3. AML/CFT (where our Services involve financial activity)
3.1 We apply a risk-based program aligned with Hong Kong’s Anti-Money Laundering and Counter-Terrorist Financing Ordinance (Cap. 615) and regulator guidelines, including customer due diligence (CDD), ongoing monitoring, record-keeping, and suspicious transaction reporting where applicable. We also follow sector-specific guidance (e.g., HKMA, SFC, Companies Registry) where relevant.
4. International Data Transfers
4.1 Although PDPO section 33 (cross-border transfer) is not yet in force, we adopt equivalent safeguards: transfer risk assessments, contractual protections (PCPD Recommended Model Clauses), and due diligence on recipients.
4. International Data Transfers
4.1 Although PDPO section 33 (cross-border transfer) is not yet in force, we adopt equivalent safeguards: transfer risk assessments, contractual protections (PCPD Recommended Model Clauses), and due diligence on recipients.
5. Security Controls
5.1 We maintain administrative, technical, and physical safeguards designed to protect data: access controls and least-privilege; encryption in transit; secure key management; network security; vulnerability management and patching; development lifecycle security; third-party risk management; backup and business continuity; employee security awareness training; and incident response procedures consistent with PCPD breach-handling guidance.
5. Security Controls
5.1 We maintain administrative, technical, and physical safeguards designed to protect data: access controls and least-privilege; encryption in transit; secure key management; network security; vulnerability management and patching; development lifecycle security; third-party risk management; backup and business continuity; employee security awareness training; and incident response procedures consistent with PCPD breach-handling guidance.
6. Data Breach Response
6.1 Our plan follows PCPD guidance: identify and contain, assess risk, consider notifying PCPD and affected individuals, and document the incident and remediation. We will act promptly and transparently.
6. Data Breach Response
6.1 Our plan follows PCPD guidance: identify and contain, assess risk, consider notifying PCPD and affected individuals, and document the incident and remediation. We will act promptly and transparently.
Join Us Today
Fast. Reliable. Settled.
Fast. Reliable. Settled.
Join Us Today
Fast. Reliable. Settled.
Fast. Reliable. Settled.
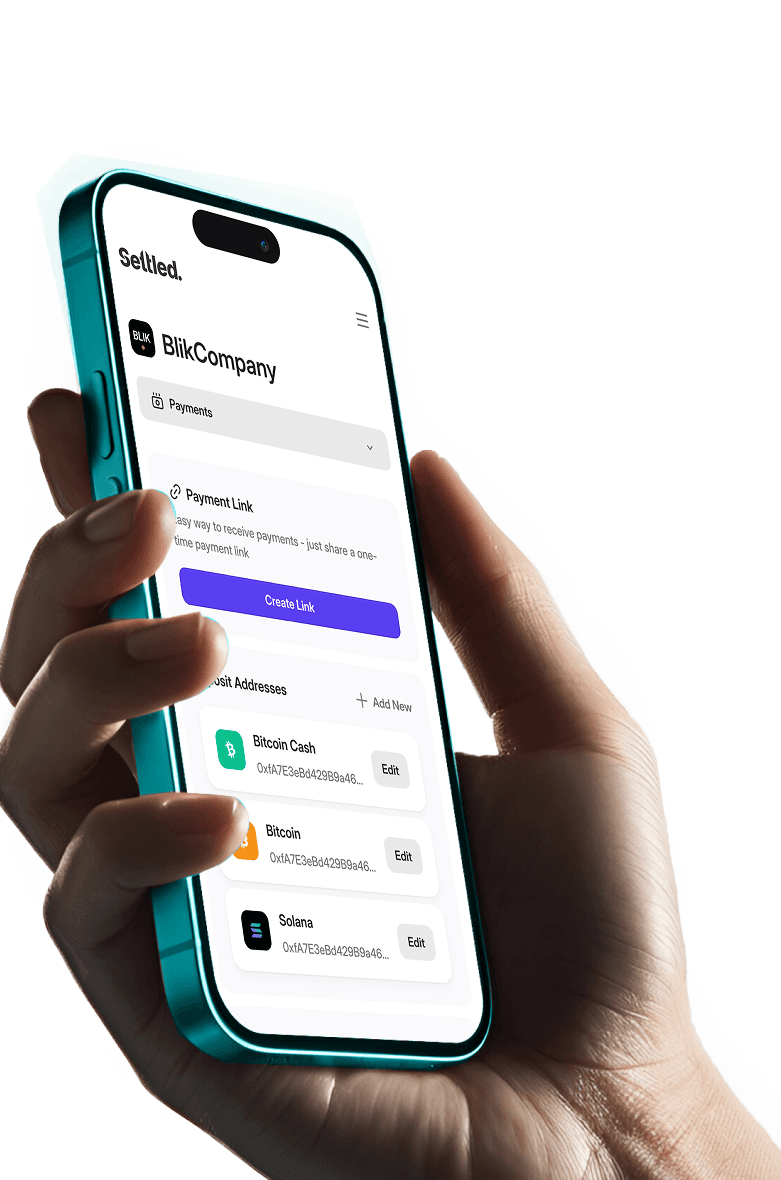
Join Us Today
Fast. Reliable. Settled.
Fast. Reliable. Settled.